The following article is written based upon information found on the NIST CSF website (http://www.nist.gov/cyberframework/) and practical experience learned by applying the Framework in the field with clients.
Introduction to the NIST CSF
For those of you who are new to the NIST CSF; NIST stands for the National Institute of Standards and Technology and CSF stands for Cybersecurity Framework. People who use the NIST CSF often refer to it simply as the “Framework”.
At the direction of Executive Order (EO) 13636, Improving Critical Infrastructure Cybersecurity, in February 2013, the NIST working with public and private sector experts, developed the voluntary NIST CSF (or “Framework”).
According to NIST; “The Framework is voluntary guidance, based on existing standards, guidelines, and practices, for critical infrastructure organizations to better manage and reduce cybersecurity risk. In addition to helping organizations manage and reduce risks, it was designed to foster risk and cybersecurity management communications among both internal and external organizational stakeholders.”
Furthermore, the Framework is “a risk-based approach to managing cybersecurity risk, and is composed of three parts: the Framework Core, the Framework Implementation Tiers, and the Framework Profiles”.
Emphasis was added.
NIST CSF is voluntary guidance
There is no specific law or written requirement that an organization use the Framework, at least according to NIST; however, this does not mean you won’t be required to use the Framework by others. Some organizations are requiring the use of the Framework by their vendors and some regulators are strongly encouraging (basically requiring) the use of the Framework. The Federal Financial Institutions Examination Council (FFIEC) has mapped financial institution regulatory controls to the Framework and so has the Office for Civil Rights (OCR) in healthcare.
Sources:
- Appendix B: Mapping Cybersecurity Assessment Tool to NIST Cybersecurity Framework (https://www.ffiec.gov/pdf/cybersecurity/FFIEC_CAT_App_B_Map_to_NIST_CSF_June_2015_PDF4.pdf)
- Addressing Gaps in Cybersecurity: OCR Releases Crosswalk Between HIPAA Security Rule and NIST Cybersecurity Framework (http://www.hhs.gov/hipaa/for-professionals/security/nist-security-hipaa-crosswalk/index.html)
The Framework is voluntary, but sort of. Good information security is not.
NIST CSF is based on existing standards, guidelines, and practices
The Framework itself is available here; http://www.nist.gov/cyberframework/upload/cybersecurity-framework-021214.pdf. The current version is 1.0. The standards, guidelines, and practices that are most often referred to are the “Informative References” found in the Framework Core. These standards are:
- CCS CSC – the “Council on CyberSecurity Top 20 Critical Security Controls”; now known as “CIS Critical Security Controls”. Available for download here; https://www.cisecurity.org/critical-controls/
- COBIT – Control Objectives for Information and Related Technology (COBIT) is a framework created by the Information Systems Audit and Control Association (“ISACA”) for information technology management and governance. Available for download here; http://www.isaca.org/cobit/pages/default.aspx
- ISA/IEC-62443 – a series of standards developed by the International Society of Automation for industrial automation and control systems security.
- ISO/IEC 27001:2013 – a popular information security standard maintained by the International Organization for Standardization and the International Electrotechnical Commission. The standard is available for purchase here; http://www.iso.org/iso/catalogue_detail?csnumber=54534
- NIST SP 800-53 Rev.4 – also a popular standard provided by NIST titled “Security and Privacy Controls for Federal Information Systems and Organizations. This standard is available for download here; http://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-53r4.pdf
It was important for the Framework to reference existing standards to lend credibility to the Framework itself, for prescriptive guidance, and for measurement. The references do provide great guidance, but also provide some of the most significant confusion.
TIP: Do not use any one Informative Reference (standard) as a checklist for implementation.
NIST CSF was developed to better manage and reduce cybersecurity risk
The key word in this statement is risk. In order to use the Framework, it is imperative that you gain a solid understanding of what risk is. In layman’s terms, my definition of risk is the likelihood of something bad happening combined with the resulting impact.
The question I constantly ask myself is “Where there is a lack of control (a gap or vulnerability), what is the likelihood of something bad happening, and what would be the resulting impact to the organization?”
Risk is a simple concept, but it is often missed.
NIST CSF was designed to foster risk and cybersecurity management communications
Adoption of the Framework is a collaborative effort and gives an organization the basis for a common set of terms, techniques, and measurements. A collaborative effort means that you will need to seek and obtain input from various stakeholders throughout the organization. You won’t be able to effectively adopt the Framework by working on it yourself or within a single group.
There’s that key word again; “risk”.
NIST CSF is designed for internal and external organizational stakeholders
The Framework is public and available for anyone to study. As adoption of the Framework becomes more widespread, more people should be speaking the same security “language”. Adoption of the Framework helps an organization explain the status of their security program to others; both internally and externally (with regulators, customers, partners, shareholders, etc.).
NIST CSF is a risk-based approach to managing cybersecurity
This is now three times that we have mentioned “risk” in this article. There’s a good reason; risk is the only viable option from which to base an information security program. The other option that people try to adopt is a control-based security program. Control-based security programs are ones where the organization identifies controls (usually based on a standard) and chooses to adopt the control because the standard says so. Control-based security programs are doomed to failure because they are expensive and ineffective.
NIST CSF is made up of three parts; the Core, Implementation Tiers, and Profiles
The following definitions are provided by NIST:
- Core – “provides a set of activities to achieve specific cybersecurity outcomes, and references examples of guidance to achieve those outcomes. The Core is not a checklist of actions to perform.”
- Implementation Tiers – “provide context on how an organization views cybersecurity risk and the processes in place to manage that risk. The Tiers range from Partial (Tier 1) to Adaptive (Tier 4)”
- Profiles – “enables organizations to establish a roadmap for reducing cybersecurity risk that is well aligned with organizational and sector goals, considers legal/regulatory requirements and industry best practices, and reflects risk management priorities.”
Core
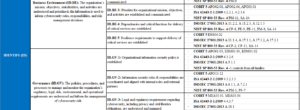
The Core is made up of four elements:
- Functions – there are five (5) Functions; Identify, Protect, Detect, Response, and Recover
- Categories – each of the five Functions is further divided in to Categories
- Subcategories – each of the Categories is further divided in Subcategories
- Informative References – each Subcategory is supported by one or more Informative References (standards, guidelines, and practices)
Implementation Tiers
The Tier selection process considers an organization’s current risk management practices, threat environment, legal and regulatory requirements, business/mission objectives, and organizational constraints. There are four Tiers:
- Tier 1: Partial
- Tier 2: Risk Informed
- Tier 3: Repeatable
- Tier 4: Adaptive
Some people equate the Tiers to maturity; however, this is not entirely accurate. See the Framework document (http://www.nist.gov/cyberframework/upload/cybersecurity-framework-021214.pdf) for full definitions and use of Tiers.
Profile
According to NIST, a Profile “is the alignment of the Functions, Categories, and Subcategories with the business requirements, risk tolerance, and resources of the organization”.
Profiles are used to measure the implementation of the Framework using a Current Profile and comparing it against a Target Profile. More information about Profiles can be found in the Framework document (http://www.nist.gov/cyberframework/upload/cybersecurity-framework-021214.pdf).
Adoption
Now that you know a little more about the Framework itself, how would you adopt it as your method of managing information security?
There is a ton of guidance available for implementing the Framework. A simple search for “implementing NIST CSF” on Google returns more than 54,000 results. Sometimes the wealth of advice is overwhelming. Let’s start simple.
At a high-level:
- Become the NIST CSF expert. There are plenty of resources for learning about the NIST CSF, but start with the source (http://www.nist.gov/cyberframework/).
- Obtain management buy-in. You will likely face plenty of opposition during your implementation of the NIST CSF and without selling to executive management, your efforts will most likely fail.
- Assemble an NIST CSF Implementation Team. Your team will help coordinate and champion the implementation effort.
- Conduct a Framework Implementation Gap Analysis; essentially creating your Current Profile.
- Define you Target Tiers; essentially creating your Target Profile.
- Conduct risk assessments where there are significant differences between your Current Profile and your Target Profile.
- Prioritize risks and adjust Profiles (Current and/or Target as needed).
- Develop and implement management processes for ongoing maintenance of the Framework (it’s iterative).
The detailed steps involved in the implementation of the Framework will vary from organization to organization. Covering each of the steps in detail is cause for a follow-up document (to this one) or a book.
Five things – How not to use the NIST CSF
Now that we’ve been using the Framework for a couple of years, we have some tips for things to avoid:
- Do not try to adopt the Framework by yourself. Adoption of the Framework requires the input and consideration of various people within the organization and cannot be effectively implemented by one person or small group.
- Do not think of adoption as ever really being done. Information security is a lifecycle discipline and you’re never really done. Treat the adoption of the Framework the same way. It will require ongoing maintenance.
- Do not try to adopt controls for the sake of controls. This may be the #1 most common error in adoption of the Framework. The Informative References in the Core are only informative references, not a list of mandated controls. The proper way to use the Informative References is to use them as a reference for a possible control that fits the Subcategory in your environment. If/where there are gaps between an Informative Reference and the Subcategory, conduct a risk assessment to determine if the control is even necessary. Remember, all well-run information security programs are built on risk NOT controls.
- Do not think that the Framework is only for “Critical Infrastructure” organizations. Although the title of Executive Order 13636 is “Improving Critical Infrastructure Cybersecurity”, the Framework can apply to almost any organization.
- Do not think that there is only one way to implement the Framework. Information security is not a one-size-fits-all discipline and either is implementation of the Framework. There are numerous guidance documents available to help you decide on the best way to implement the Framework into your environment.
Questions?
Books can be written on the details for implementation of the NIST CSF. We hope that this document provided enough guidance to get you started, but if you still have questions, contact FRSecure. We’ll be glad to assist.







Thanks Evan for putting it in simple words for someone trying to make sense of CSF.