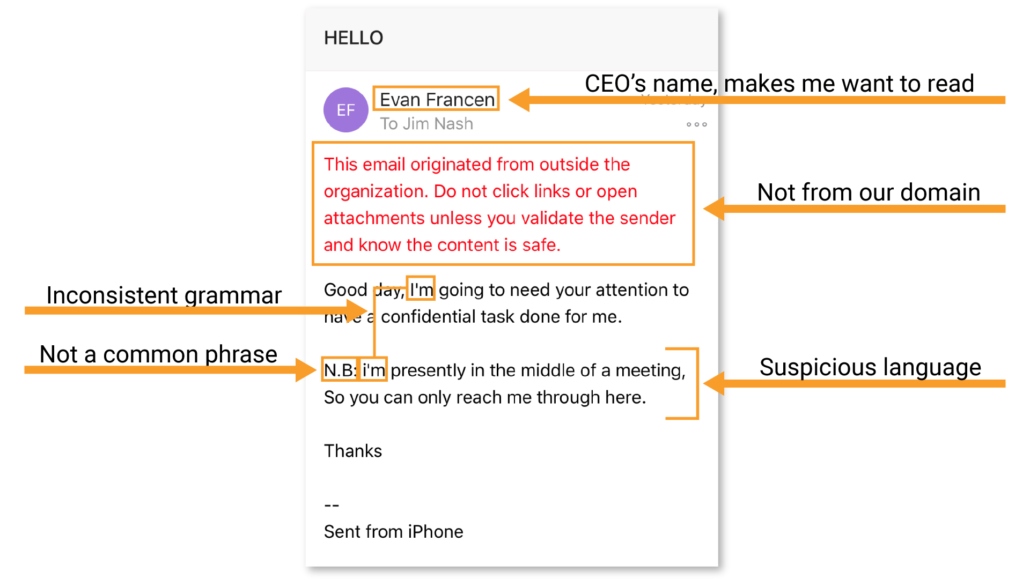
I got this email in my inbox recently. Since it had our CEO’s name on the sender line, I looked at it right away. It was clear in about 20 seconds that it WASN’T from him, and that it should be deleted and immediately reported as spam.
Emails like this are dangerous if not handled properly, but they also act as fantastic teaching materials.
Before I deleted it, I screen captured the image to show the ways threat actors and criminals try to steal from you. Spear phishing is an email that relies on perceived urgency and emotional response, but if you train yourself to check a few things before blindly obeying, you should increase your odds of evading the trap.
Let’s look at the email in two forms and walk through the things that tipped me off. These are the same things you should begin looking at as you get emails that appear to be from people within your organization.
1. The first thing that I noticed when opening the email was the warning from our email provider that alerted me to the fact that this email originated from outside my company.
It made me raise my eyebrow in suspicion initially, but given that I’ve known our CEO, Evan, for 19 years, I figured it was reasonable for him to send me something from his private email. Normally, if you see this warning, it did not come from someone within your organization, and you should be wary about replying or clicking links without further investigation.
2. The greeting line of “Good day” is not something my boss (and good friend) would ever say to me. Evan would not greet someone in person like this, so he certainly wouldn’t start off an email in this way either.
While I have known him for a long time, you should look at the grammar and word choice of the emails you receive and see if you can find clues as to whether this is something that the person who the email is seemingly coming from would legitimately write or say.
3. The body of the first sentence is peculiar as well.
“I’m going to need your attention to have a confidential task done for me.”
This, in conjunction with everything else I’ve uncovered thus far, is making me realize that this is a hoax. Evan would never ask me to do something like this, nor would he ask me in this manner. Evan is traditionally an open book and doesn’t ask people to do things that he isn’t willing to do himself. You should know the type of language your boss (or coworkers) would use and compare it to the language in any email asking you to do something like this.
4. The second paragraph has some giveaways as well.
a. “N.B.” is a Latin abbreviation for Nota Bene. This phrase that indicates something is important.
b. “I’m presently in the middle of a meeting, So you can only reach me through here.”
The use of a Latin abbreviation is something that I KNOW Evan would never ever use. I even had to look it up. This is certainly an indication that this is from another country because it is stylistically very different from what we would send to each other in our organization—and in our country, really.
Additionally, the mis-capitalization, and capitalization of certain words is a good indication that this is someone for whom English isn’t their native tongue.
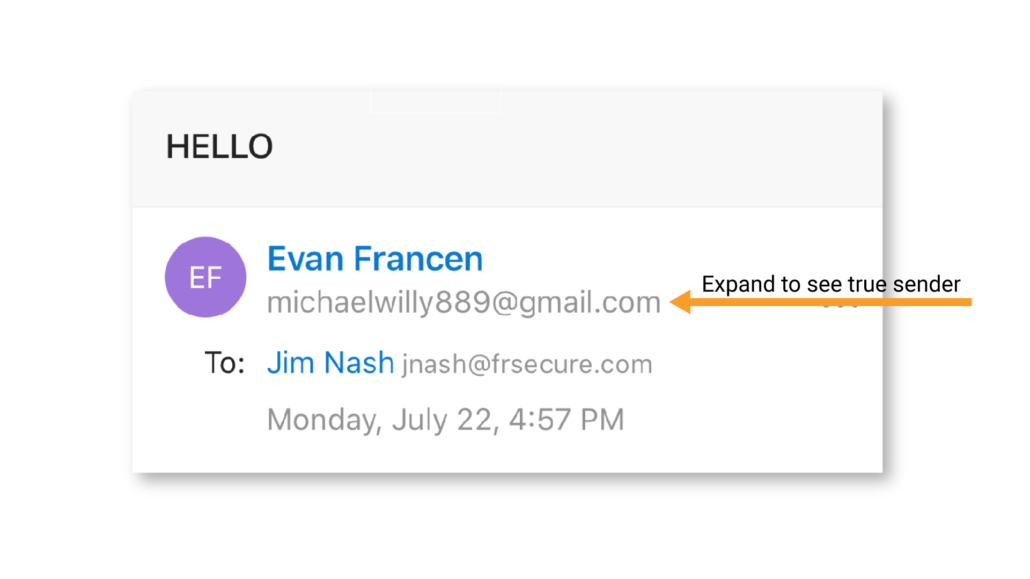
There is one final tip that can easily and quickly help you identify if the email truly is not from the person that it claims to be and therefore should not be acted on. You can reveal the actual email address of the sender.
If you look at the image below, it shows how you can expand the area with the sender information to include their email address, and not just their full name. Names can easily be doctored, but the email address usually cannot.
The email address that should be Evan’s actually belonged to a scammer sending from, . This simple habit of clicking or expanding the box around the sender’s email name to reveal the email address can help you uncover if the person sending the email is actually who they claim to be. If this clearly (as in my case here) isn’t from your boss, you should screenshot the email, delete it, and send the screenshot to the person who is being impersonated, as well as your internal cybersecurity team. Doing so makes them aware of the scam and allows them to help others understand that they haven’t sent any emails like this and to look out for it.
This type of social engineering technique is called a spear phishing attack. It’s an attempt at gaining access to someone’s personal information using a very targeted and specific approach. It is a common occurrence in the U.S., and it happens virtually every day. Because of that, you should become familiar with the tricks that these criminals use to get people to fall prey to their attacks.
Please share this article so your friends and colleagues can learn how to identify a spear phishing attack email, and don’t hesitate to reach out to us with any questions or for help improving your information security program, training, and practices.