In case you haven’t heard, phishing is VERY popular among the hacking set right now. Attackers are using phishing emails as an easy means to acquire credentials to break into networks or to download malware in order to take control of networks or steal (or ransom!) valuable information.
If you are knee-deep in information security, you might feel like you’ve become a bit worldly-wise about how to detect phishing emails. If you are anything like me, you likely ignore about 70% of legitimate emails from co-workers, friends, and family because they fall into that “look suspicious” category (you know the ones, with a generic subject line like “Check this out!” and only a link to an interesting article in the body of the email).
But most of us have yet to turn paranoid about scrolling through our inboxes and are less likely to know the signs of an attack or even know how to validate email addresses when concerns are raised. And while there are many ways in which attackers create and send phishing emails, there are a few best practices every user should know and use to help sort out the real messages from the fake ones.
How To Check If An Email Is Legit
There are a few common things to look for when trying to determine the legitimacy of an email. Implementing these three common practices will go a long way to protect you from inadvertently sharing your password with an attacker, sending all of your personnel W-2s to cybercriminals, or wiring funds to some crime syndicate.
Verify
The easiest, and still one of the most effective, ways to protect yourself is to validate the email address identity.
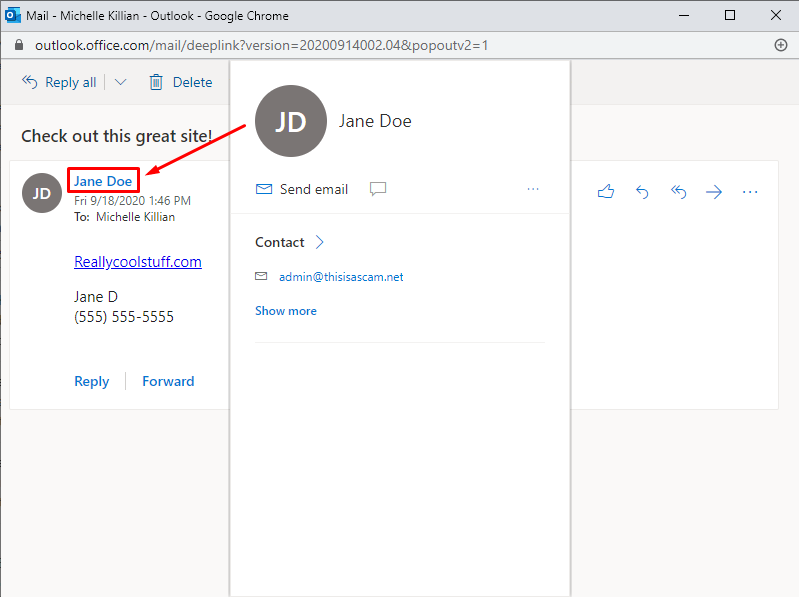
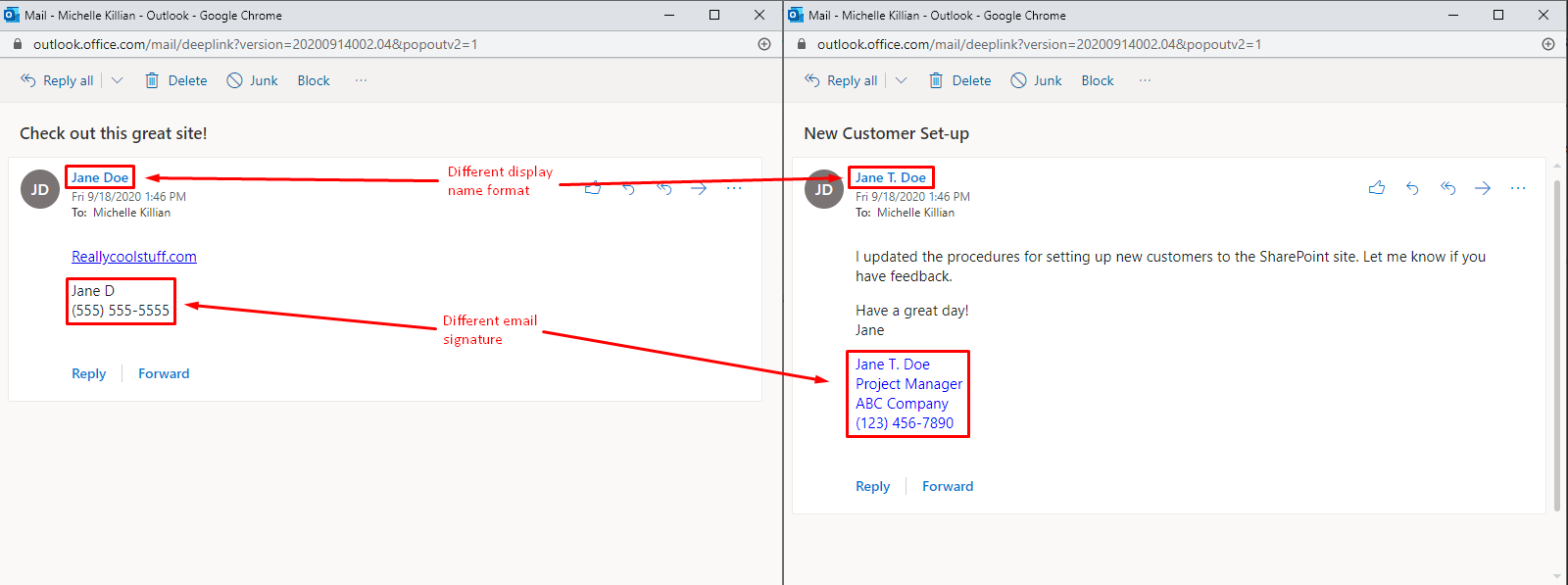
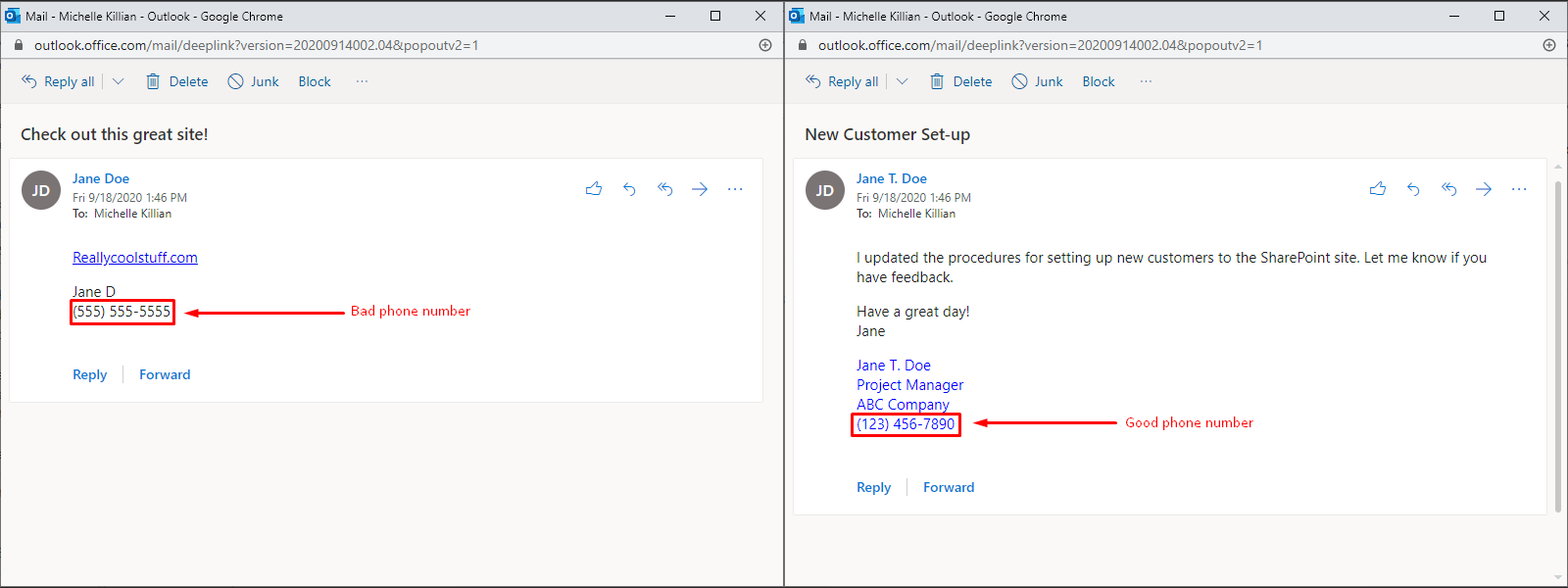
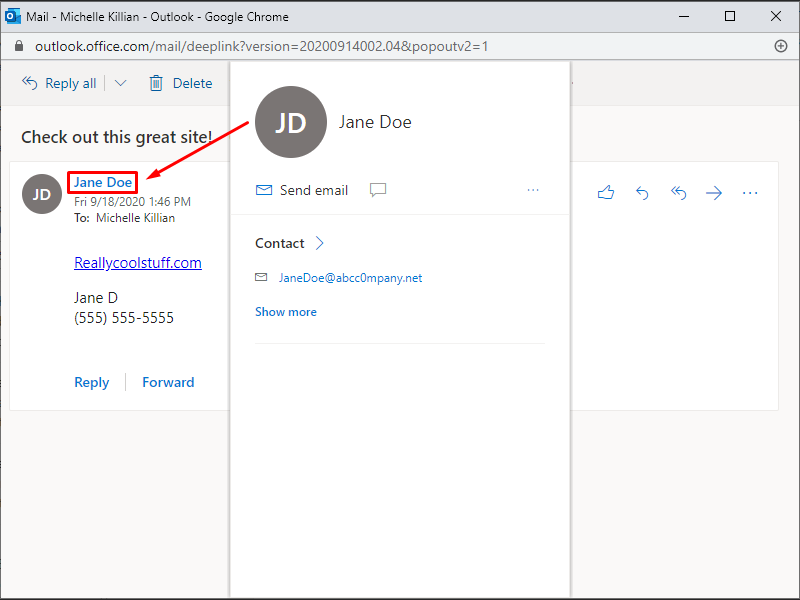
First, hover over the “from” display name to see what email address pops up (to hover, move your pointer over the information that you want to verify). It’s very common for an attacker to spoof a display name to look like it is coming from someone legitimate, but when you hover over the display name you’ll often find that message is actually coming from someone else.
Still not convinced? If the email is coming from someone you regularly communication with, compare the new message against older ones. Does the display name look the same for all emails? Is the email signature the same?
And, lastly, don’t forget to call! There’s nothing like a good old-fashioned, pick-up-the-phone and ask the person if they meant to send you the “I’m stuck in Paris and need money to get out now” message – just make sure you use a phone number from your address book and not one on the potentially suspicious email.
Inspect
Some attackers work a bit harder and make it a bit trickier to expose their scam. For these, you need to dig a little deeper.
Remember when we hovered? Let’s go back to the email that showed up and take a closer look. Many times the attacker will employ a slight-of-hand (like magicians do) so you think you are reading an email address correctly but they’ve actually switched out, added or replaced characters (commonly known as substitution and transposition). It’s common to see legit email addresses with an “m” replaced with an “rn”, a lower case “L” switched out with the number “1” or a .com email reading as .co instead. Even the slightest change in an email address means the email is going somewhere else.
Hopefully, your IT team has enabled Sender Policy Framework (SPF) Records in your email system, but just in case, check the internet header information to see where the email is going to. As an added bonus, this makes for a great party trick and will make all your friends think you are a technical genius!
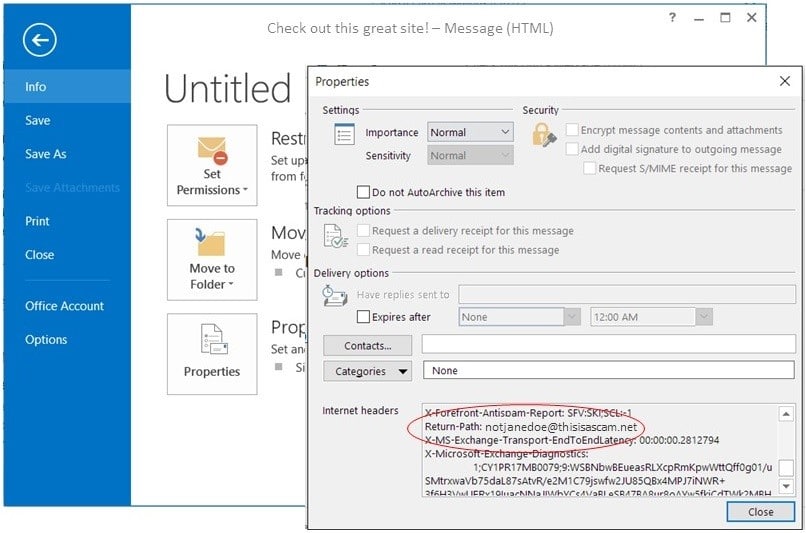
To find the properties in an email (using Microsoft Outlook), click File>Properties and look for the “Return Path” or “Reply To” in the Internet headers section
Search
Another great way to find out if a sender is legitimate is to do a search on the email domain – this is especially useful for messages you receive from new contacts or people you aren’t as familiar with.
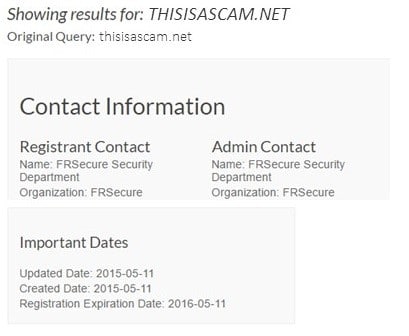
Verify the domain name ownership and set-up details. Sites like WHOis and ICANN allow you to find out details about when a domain name was set up and often, who the owner of the site is. If a site was created in the last 90 days but the promising new vendor tells you that they’ve been in business for the past three decades, you might want to question the legitimacy of the message.
Google (or Bing! Or Yahoo!) it. The search engines are really pretty diligent about making scams visible and getting them to the top of the search results when they have awareness of them. If you have doubts about a message, do a quick internet search to see if anyone else has reported the message as a scam.
Other Clues to Watch For
In addition to trying to verify the legitimacy of the sender, there are other common clues to be on the look-out for in the body of the email, including:
- Unusual grammar or phrases: Does the email message seem a tad bit too polite for this particular co-worker? Then odds are, it’s not him.
- Emails sent at odd times: If you are used to getting invoices from a vendor on the first of the month but get one in the middle of the month, it’s worth questioning. Similarly, if you have a client who consistently emails you only from 8-5 but suddenly sends you a message in the middle of the night, it might be worth a follow-up call to verify she sent the message (and to ask why on earth she was working at midnight!).
- A sense of urgency to respond: Is the message unusually pushy, asking for immediate action (often paired with some sort of dire consequence if you don’t respond)? Don’t take the bait and act out of panic.
- The link in the email doesn’t match the destination address: Remember that hover trick we used to verify the sender’s email address? Use that to verify the links that show up in the email message are pointing to the same web address that you’ll go to when you click on the link. (If you are viewing from your phone, try holding down your finger on a link to get the same pop-up.)
And, finally, learn to trust your gut. If something seems amiss, it probably is.
*All images and domains used in this article are fake. We do not own ThisIsAScam.net or ABCCC0mpany.net. Please do not click on emails from either of these domains unless you know who the sender is.







How do I verify that the email id is not from a scammer? eg he creates a email id sounding similar to an actual company. eg Helifax Oil and gas has an email = ; which is posted on their website.
The scammer may send an email from “’ giving a fantastic job offer.
Thank you, it’s very helpful to be able to spot suspicious emails.
Phishing emails are a growing threat, and this article highlights simple yet effective practices to verify email legitimacy.
Hovering over display names, comparing past emails for inconsistencies, and using trusted phone numbers to confirm suspicious messages are excellent tips. Staying vigilant and taking these small steps can prevent falling victim to cybercriminals’ increasingly sophisticated tactics. Awareness is key!