It’s that time of year again. Perhaps like you, I’ve seen dozens of articles written by our industry “experts” about what to expect in the year ahead. The outstanding folks here at FRSecure asked me to write my own 2018 information security predictions, so here they are.
What do I think is going to happen in 2018?
Hold on a second. Before we jump into next year, let’s take a quick look in the rear-view mirror. Like most years, 2017 was a crazy year that deserves some review.

Quick 2017 Recap
In 2017, the hacking group known as the Shadow Brokers made a name for themselves with their April release of (alleged) NSA tools (including EternalBlue). Ransomware became even more mainstream, at least in the news, with the WannaCry outbreak in May. Arguably the biggest news of the year was the Equifax breach and all the related hoopla. Hands down, the Equifax breach takes the prize for the worst breach of 2017, and the worst breach response in history. Although Equifax was a very newsworthy breach, it wasn’t the only impressive (or depressive) breach of the year:
- Deep Root Analytics – 198,000,000 U.S. citizens affected (voter registration data)
- Yahoo – not really a breach in 2017, but we learned a lot more about the 2013 breach that affected more than 1,000,000,000 accounts.
- Uber – 57,000,000 Uber users affected and a ridiculous story to boot.
- Kaspersky Lab – suffered a hack at the hands of Israeli intelligence officers, became embroiled in the “red scare” related to Russian hackers targeting U.S. elections, and now suffers from a full-fledged U.S. government-wide ban on all Kaspersky products. You could make a movie out of this.
Some of the other more noteworthy names in the news this past year for not-so-good reasons (breaches or other) included E-Sports Entertainment Association (ESEA), Xbox 360 ISO and PSP ISO, InterContinental Hotels Group (IHG), Arby’s, Verifone, Dun & Bradstreet, Saks Fifth Avenue, America’s JobLink, FAFSA: IRS Data Retrieval Tool, Chipotle, Gmail, Brooks Brothers, DocuSign, Kmart, University of Oklahoma, Washington State University, Verizon, U.S. Securities and Exchange Commission (SEC), Deloitte, Sonic, Whole Foods Market, Disqus, Hyatt Hotels, Forever 21, and Imgur.
What used to be an exclusive club has sadly become the opposite.
Information Security Predictions for 2018
OK, now the look ahead. Beyond expecting more of the same security nonsense, these are the things that I think will happen in the coming twelve months.
NOTE: If you want to skip all the words and just get to the list of predictions, go here.
1. The General Data Protection Regulation (GDPR). It really is a big deal.
This will be mostly positive I think, depending on your perspective. The GDPR was approved in the Spring of 2016 and finally goes into effect (enforcement) on May 25, 2018. The regulation protects European Union citizens, but its impact will be seen globally. Any organization anywhere that is involved with serving customers (or employees) in the EU will be directly impacted. Organizations who are not compliant will face hefty fines, and there are strong signs that EU member states will vigorously enforce the GDPR.
What to expect in 2018
Expect the EU to set the tone for enforcement early and often. There will be more than one organization to be penalized for non-compliance, and I expect the EU to set an example with one or more of these first offenders. The example set by the penalties will receive global attention and accelerate GDPR compliance plans for organizations who have/had not taken it seriously.
I think GDPR is going to be a big deal in 2018, and I think that other non-member countries will seek similar regulations in future years.
2. Ransomware attacks will continue and will become more sophisticated.
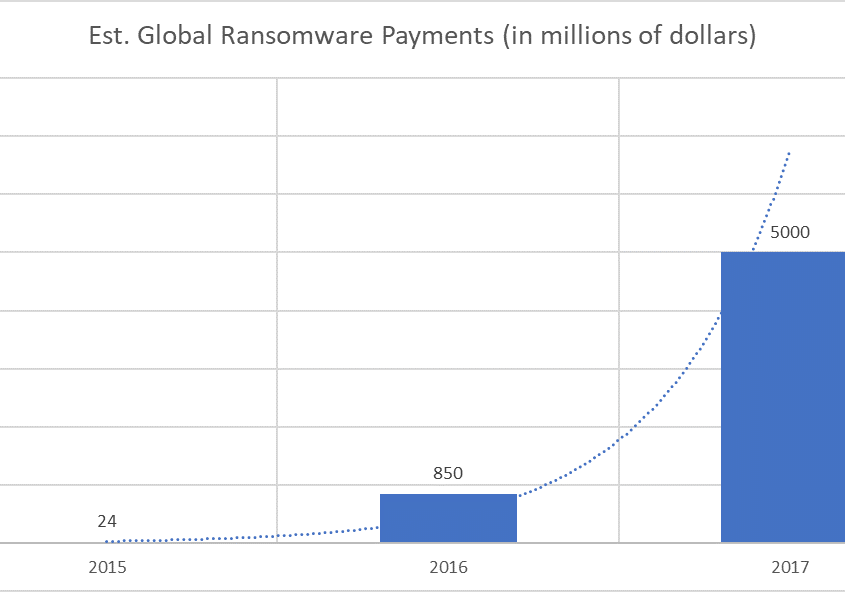
Most of us have known about ransomware attacks for a long time but these types of attacks have become more popular when the attacker’s return on investment for payment card (debit/credit) attacks began to decline. Ransomware attacks were very lucrative for attackers in 2016 and 2017, and the return on investment is still quite high. When ROI is high, expect more attacks. What won’t be the same are new(er) and more sophisticated techniques.
What to expect in 2018
Organizations have gotten better at protecting themselves from ransomware. We’re slightly better at prevention and markedly better in response. The combination of these things means that attackers are getting paid less often, but also means that they’ll probably just step up their game. Expect ransomware that doesn’t really go away easily (even after paying the ransom). Expect ransomware that exfiltrates data; this way, even if you restore from backup, the attacker is still holding your data ransom (potentially for public release or some other use). Expect ransomware that you can’t detect; you’ll notice the symptoms of the attack, but you won’t easily find the cause because the ransomware is file-less.
3. IoT attacks will get nasty.
The IoT attacks we’ve seen in 2017 were mostly DDoS-related. These attacks are very annoying, but in most cases, the annoyance ends when the attack ends. There are billions of devices, cars, home appliances, medical implants, biochip transponders, etc. that make up today’s Internet of Things (IoT) landscape. Function and convenience have always been the IoT king; security was/is an afterthought. This is an attacker’s playground and the opportunities for exploitation are seemingly endless.
What to expect in 2018
Cyber-hijacking will become mainstream in 2018. There will be at least one high-profile and successful cyber-hijacking attack in the coming year. An attacker will take full control of an IoT network (think industrial automation and control system), and cut the owner out of the system. A ransom payment will be required for the owner to regain control. I also think that we’ll see news of successful attacks against more consumer electronics (televisions, appliances, etc.).
4. More financial fraud attacks through partners.
We have seen an increase over the last six months in attacks that happen through a partner that was previously compromised. An attacker compromises your partner, then uses your partner’s systems to attack you. The target for these attacks is money through financial fraud.
An example scenario looks sort of like this:
- Your supplier is exploited.
- The attacker has obtained access to one or more user accounts.
- The attacker sends an email to your accounts payable using the compromised email account of the supplier’s accounts receivable department. In the email, the attacker states something like “Dear Jane, I am writing this email to inform you that XYZ Supply Co. is no longer accepting checks for payment of outstanding invoices. Our preferred payment method is now ACH. Would you please inform me of the proper process (or paperwork) that needs to be completed to make this change on your end?”
- Your accounts payable person responds to the email informing the supplier (actually the attacker) that he/she will need to complete the attached payment modification form and send it back signed.
- The attacker complies and sends the completed modification form (along with the ACH information) to your accounts payable person.
- Your accounts payable person processes the change in the system.
- The attacker sends new invoices that have been copied from the supplier’s previous emails.
- Your accounts payable person sends payments, everything appears normal.
- The unauthorized payments aren’t noticed for weeks, usually when the legitimate supplier asks you when they can expect payment (because the attacker intercepted invoices and got the money).
Ugh. It’s a mess, but we’re seeing an increase in these attacks and the return on the attacker’s investment is very good. In one case this past Fall, the attacker got away with more than $800,000.
What to expect in 2018
These attacks don’t make the mainstream news very often. There’s rarely any legal obligation for victim organizations to report these attacks to anyone. Reporting these attacks to law enforcement (either local or FBI) doesn’t get much attention either. I think these attacks will get more attention in 2018 because there will be an increased frequency and impact. There are organizations that are going out of business because of these attacks, and banks are losing money too. These silent attacks will become less silent.
We trust our partners, but we shouldn’t trust their security as much as we do.
5. The lack of qualified security expertise problem gets worse; outsourcing of security services will grow.
The information security labor market looks bleak unless you’re a job candidate. Cybersecurity Ventures predicts that there will be 3.5 million unfilled positions globally by 2021. The unemployment rate for people in our industry was 0% in 2016 and is expected to remain at 0% through at least 2021. Two out of three high schoolers say the idea of a career in cybersecurity had never been mentioned to them by a teacher, guidance or career counselor, according to Raytheon. The Occupational Outlook Handbook (Bureau of Labor Statistics) claims that the job outlook from 2016 – 2026 is 28% growth annually or “much faster than average.”
This is great news for an information security professional or somebody wanting to become one. This is terrible news if you’re a company looking to hire one of us.
What to expect in 2018
We expect significant growth in two areas:
- Outsourced information security services – By some estimates, the market itself is expected to increase between 15 – 24% annually. The fastest growing service from FRSecure has been our virtual Chief Information Security Officer (vCISO), and we expect the growth to continue beyond our 40% projections.
- Free information security training and certification classes – FRSecure has been a pioneer in this effort since we started the CISSP Mentor Program in 2010. In 2010, we started with six students and last year we had more than 160! We expect another jump in the growth of this program to more than 300 students in 2018. Not only do we expect more growth for the CISSP Mentor Program, we expect to see a trend with other organizations in our industry following suit. Each class and each student should be seen as a contribution to fixing this issue.
6. Cryptocurrency chaos; attacks, price volatility, and regulation.
Bitcoin isn’t new, but to the mainstream it is. In 2013, there were an estimated 300,000 to 1.3 million bitcoin owners; however, the exact number is not known because one person can own multiple bitcoin wallets. In 2017, there are an estimated 2.9 million or more bitcoin owners; some estimates are as high as 5.8 million.
The “genesis block” (or first ever block in the chain/start of bitcoin) was January 2009. Bitcoin is/was very popular amongst people who want anonymity in financial transactions, which just so happened to be criminals; most of whom operate businesses in the Darkweb. Soon exchanges began open, people were trading bitcoin, values soared (and declined), and traditional money (U.S. Dollars) began to flow into the currency.
The value of bitcoin since January 2015 has risen from $287 to a peak of more than $19,000 in December 2017. The huge increase in value has brought all sorts of investors out of the woodwork. I’ve heard stories of people moving whole retirement accounts into bitcoin, and people mortgaging their homes (1st and/or 2nd mortgages). Only with great risk comes great reward, or so logic would say.
What to expect in 2018
I have three predictions for bitcoin/cryptocurrency in 2018; more newsworthy attacks, price volatility, and a strong push for regulation.
More Newsworthy Bitcoin Attacks
There are two solid justifications for this prediction:
- People are generally flawed. Like most problems we have in information security, it’s not the technology that’s the issue. It’s the implementation and management of the technology that’s the issue. I don’t know of any flaws in blockchain itself, but I do know that there are plenty of flaws in how it’s being implemented and managed.
- If there’s a lot of money at play, there’s a lot of people who want it. Where there’s money, there will also be crooks. In the earlier days (only like a year or two ago), attackers didn’t target bitcoin exchanges much because they were getting a greater return on bitcoin as a viable anonymous payment method. Now that bitcoin itself is so valuable, and other criminal enterprises have been throttled a bit, bitcoin itself is a potentially lucrative target.
Expect more attacks on bitcoin exchanges. In 2017, there were multiple DDoS attacks against bitcoin exchanges and there were stories of attacks that resulted in stolen bitcoin. Expect an increase of both attack types in 2018. Stealing bitcoin is a great return on an attacker’s investment, and the risk is relatively low.
Expect more attacks on clients. Attackers will target bitcoin wallets more than ever in 2018. If a bitcoin user loses his/her wallet or is unable to access his/her wallet, the bitcoin is gone. There is no recourse and the user will not be able to recover the bitcoin. Period. Attackers will also trick users into installing/running coin-mining software on their computers without their knowledge.
Price Volatility
Bitcoin is non-regulated and a little wild west-ish. There have been bitcoin price/value corrections in the past, but I expect some really wild price swings for bitcoin in 2018. It’s hard to fathom the extent of the speculation behind bitcoin values right now. Where there’s intense speculation, there’s a better chance of a violent correction.

Push for Regulation
The push has already started. Just this morning as I was writing this article, I read that South Korea is has announced new regulation. Expect this and more in 2018. When chaos ensues, the governments will want to step in. In some cases, regulation might be a good thing.
7. Cyber-Insurance SME market will explode.
According to Allied Market Research, the global cyber-insurance market will grow to more than $14 billion by 2022. Insurance underwriters seem to have no idea how to quantify or understand information security risk for small-to-medium sized companies, but this will start to change in 2018. Underwriting for large companies seems to be a little more scientific because of the loss data that’s available (most of the losses are public knowledge).
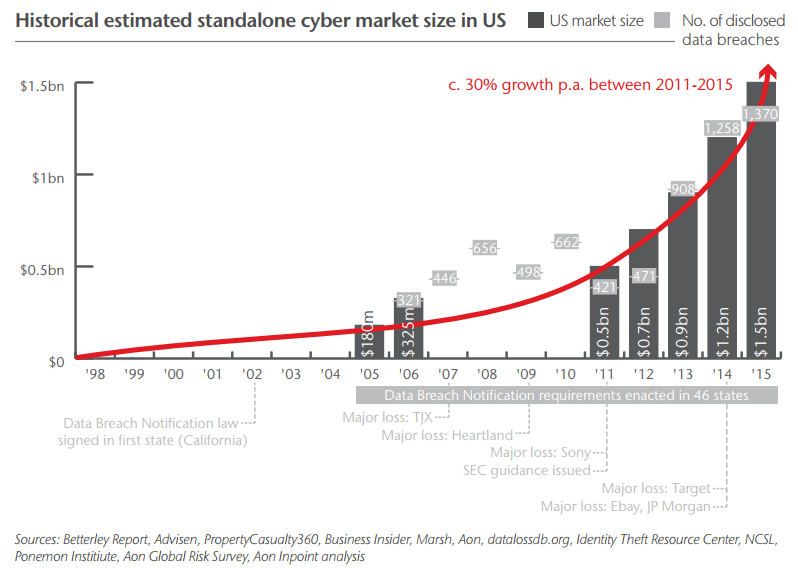
What to expect in 2018
In 2015, cyber-insurance policy premiums from SMEs accounted for roughly 19% of the entire $1.5 billion cyber-insurance market in the U.S. I expect SMEs become the largest market in 2018 (and beyond), accounting for between 34% to 38% of the total.
This is an insurance boon for insurance companies, and this is an opportunity to get much better coverage for customers. Insurance companies will start to understand information security risk better too.
8. Attacks on the US government and critical infrastructure.
There have been attacks on U.S. government interests and critical infrastructure for years (as many as 77,000 attacks in 2015 alone), but for the most part, they’ve been minor compared to what I think is on our horizon. Earlier this year there were a series of ongoing attacks on Ukraine’s power grid. It appears that Russians were behind the attacks, and the intent was to “destabilize” the region. What’s most disturbing; however, is the speculation that the Russians were using these attacks as test runs for future attacks, possibly against the United States.
What to expect in 2018
According to Andy Greenberg (a well-respected investigative reporter for Wired Magazine) who investigated the Ukraine attacks, “All of the most powerful nations in the world — U.S., Russia, China — probably have the ability to take down each other’s power grids and infrastructure, but the scary thing is that Russia is brazen enough to actually do these things.” I agree with Andy, and this is a potential scenario in 2018. More likely; however, are probing and testing types of attacks where attackers will be focusing on putting all the dots together to orchestrate a very major attack in the future. Expect an increase in successful critical infrastructure attacks in 2018, on a wider scale with minor impacts.
As far as attacks on the U.S. government, I don’t expect a significant increase from previous years (at least from what I know).
9. A breach will occur that results in loss of life.
This isn’t a popular prediction and certainly not one that I hope for by any means. It will only be a matter of time where a computer/network system breach will result in a direct loss of life. Sadly, I think it’s inevitable.
As we continue to connect anything and everything to the Internet or Internet of Things (IoT), we increase the likelihood of this scenario. We are inviting the Internet (and attackers) into our living rooms, into our cars, into our bodies (via medical implants), into our kitchens, into our bathrooms, into our bedrooms, into our children’s’ toys, into just about everything.
What to expect in 2018
I think we could see the first human life lost in 2018 that will be directly attributable to a failure in information security. It could come from a compromised medical device implant or a compromised vehicle system. If there isn’t a human life lost, there’s a strong possibility that control of one or more devices could be held for ransom.
I don’t like this prediction at all, and let’s hope I’m wrong.
10. A new law protecting U.S. citizen identities.
The Social Security number (SSN) is arguably the most sensitive piece of information related to our identities as U.S. citizens. With a compromised (or stolen) SSN, an attacker can:
- Open financial accounts in your name
- Get medical care in your name
- File a fraudulent tax refund in your name
- Commit crimes in your name
- Steal your benefits
It’s also safe to assume that the SSN belonging to every U.S. citizen has been compromised in one or more of the 100s (or 1000s) of breaches involving such information. Credit monitoring, credit freezes, and other protections are only band-aids to treat a bullet wound.
What to expect in 2018
I expect a bill to be written and a federal law to be passed that empowers U.S. citizens to protect their identities. I know for certain that the bill will be written because Brad Nigh (FRSecure Director of Consulting Services) and I are writing one right now. What I’m not certain about is if it will become law. Although politics aren’t our game, we’re going to give it a whirl in 2018.
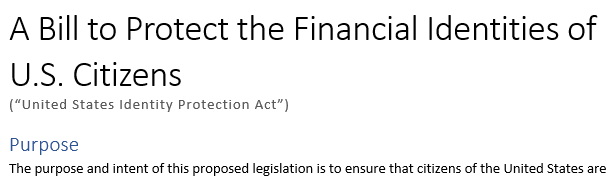
Short summary; All use of Social Security Numbers (SSN) must be accompanied by authentication under the control of the citizen for whom the SSN identifies. More to come in future writings. We’ll likely need your support to help push this through!
BONUS 2018 PREDICTION
The “Fixing a Broken Industry” book will be completed and published this year. The book covers:
- The personal journey including real-world stories of how the broken information security industry has hurt companies and real people.
- The ten ways in which our industry is broken.
- The ten things we intend to do collectively if we want to fix the industry.
Coming soon to a bookstore near you! Stay tuned.
2018 Predictions Summary
The quick and dirty. Here’s the predictions list in order:
- The General Data Protection Regulation (GDPR), it really is a big deal.
- Ransomware attacks will continue and will become more sophisticated.
- IoT attacks will get nasty.
- More financial fraud attacks through partners.
- The lack of qualified security expertise problem gets worse; outsourcing of security services will grow.
- Cryptocurrency chaos; attacks, price volatility, and regulation.
- Cyber-Insurance SME market will explode.
- Attacks on the US government and critical infrastructure.
- A breach will occur that results in loss of life (directly).
- A new law protecting U.S. citizen identities.
There you have it. Some of these information security predictions will come true, others won’t. Make 2018 a year that you protect yourself, your family, and your organization better. Like these predictions or have predictions of your own? Contact us, leave a comment, or share this blog.







I think all of these predictions are right on. However I really hope you are wrong about #9, but I can tell you it is a very real possibility.