The United States Department of Defense (DOD) is upping its security game in a big way in 2020. The government agency, which provides military forces for national security, released a new certification—The Cybersecurity Maturity Model Certification (CMMC)—at the end of January 2020 that aims to decrease the impact of cybersecurity risks that threaten the defense industry.
More and more, information security and cybersecurity efforts in organizations all over the world are impacted by a growing web of connected vendors. In turn, it has become hypercritical that organizations not only understand how mature their vendors’ security programs are but also have a hand in making them better. Otherwise, they run the risk of a compromise that (on paper) wasn’t their organization’s fault.
And that’s the basis of the CMMC cybersecurity requirements. With the CMMC, the DOD is doubling down on knowing where its vendors’ security programs stand and is using the certification as its audit framework.
If you work with the DOD as a vendor, this is on the horizon. It’ll likely change your relationship with the DOD and the way your organization needs to handle its security measures.
Here’s what we know about the CMMC so far.
What is the CMMC, Anyway?
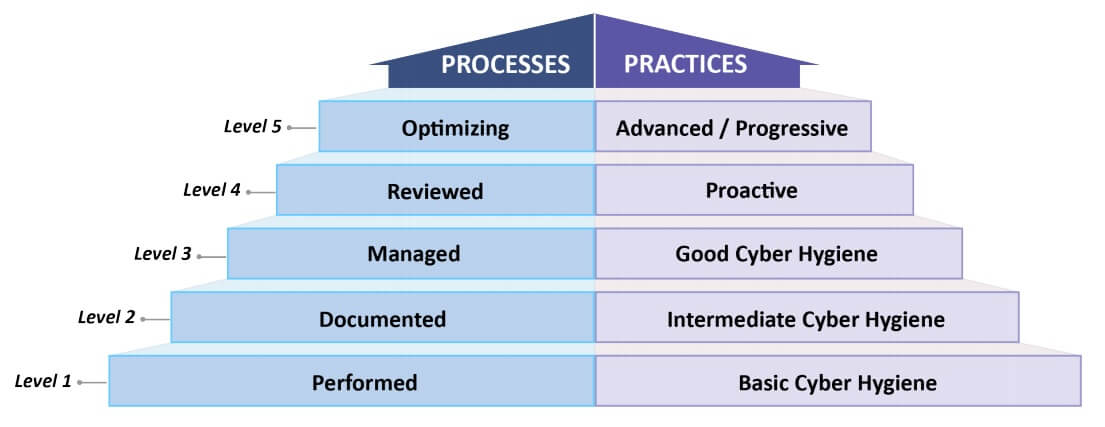
This is the government’s way of keeping tabs on the security of its potential defense vendors. It provides a mechanism for the DOD to ensure their vendors are ready (security-wise) to work with the department. It focuses on certifying the “maturity levels” and “capability” of each DOD vendor’s security processes, practices, and methods. It also helps set goals and priorities for them to make improvements.
The framework of the certification combines several known security best practices and regulatory standards (like NIST SP 800-171) and will be used primarily as a method of helping to select vendors to contract during requests for proposal (RFPs) processes. The DOD will add CMMC levels to each RFP, meaning vendors who don’t possess mature enough processes may not even be allowed to submit for that proposal.
There are 5 levels to the CMMC.
Level 1
This level focuses on basic safeguarding of information and basic cyber hygiene. While organizations in this level must be able to protect Federal Contract Information (FCI), they’ll often only be required to do so in an ad-hoc manner and will not be required to prove documentation or have their process maturity analyzed.
Level 2
A step up from level 1, level 2 focuses on intermediate cyber hygiene. The biggest difference between level 2 and level 1 is that there is a focus on the documentation of policies and practices. Organizations in this level will focus on documenting their processes with the expectation that they practice their documented processes accordingly and repeatedly. This helps with remediation and growth, acting as a transitional step for organizations looking to win contracts with Controlled Unclassified Information (CUI).
Level 3
Level 3 actually focuses on protecting Controlled Unclassified Information (CUI). In this level, there’s a higher emphasis on mitigating threats. Organizations in level 3 are expected to be able to develop and maintain a plan. The plan should include things like goals, project plans, resources, training, and more.
Level 4
Once the plan is in place, the next step is to test and measure its effectiveness. Level 4 focuses on the organization reviewing its security practices and finding gaps where it can consistently make improvements or correct inefficiencies. The ultimate goal of this level is to increase the protection of CUI and start reducing the risk of Advanced Persistent Threats (APTs).
Level 5
This level is where optimization occurs. Organizations in this level have a plan, consistently work to find and fix inefficiencies in it, and standardize and implement the plan and practices across the whole organization. The emphasis here is also to increase the protection of CUI from APTs.
The level your organization fits into will indicate the number and which kinds of practices the security program will be required to follow, and how they are validated. The practices build on each other. Level 1 contains 17 security controls, and level 5 contains 171, including all of the practices from levels 1-4. The goal is to help organizations move from basic data safeguarding to reducing APTs, but ultimately, your level as an organization will determine how (or if) you can do business with the DOD.
How Will My Organization be Impacted by The CMMC?
Effectively, if you’re a manufacturer working with the DOD, this needs to be on your radar. It’s anticipated that 350,000 vendors down the supply chain of the DOD will be impacted by these security requirments.
While none of the current requests for proposal with the DOD contain CMMC compliance requirements, the department is unveiling 10 requests for information on contracts starting in June of this year that will include them. By 2026, every request for proposal the DOD initiates will have some level of CMMC requirement.
The DOD will not be conducting its audits, either. A network of certified third-party assessors (C3PAOs) will be tasked with vetting the security of each of its potential vendors. Each of its 350,000 vendors will need one of these assessments.
What Do I Need to Do from a Security Standpoint?
Get Ahead of It
If you want to work with the DOD moving forward, this needs to be something your organization proactively considers. Sure, the actual requirements won’t begin for quite some time (especially for small- and medium-sized businesses), but good security practices are all about being prepared. So is audit prep.
More importantly, though, major changes in security programs often require changes in thinking and behavior at the organizational level. This is not something that happens overnight. To create a culture where security becomes the focus, you’ll need time.
While time feels like a luxury now, the sooner you begin making these changes, the easier it’ll be when the time for compliance comes.
Asset Management
At the end of the day, good security practices come with doing the basics right. No fancy technology or software alone can get your program where it needs to be. A risk assessment is a great start to helping guide your practices, but it’s not a silver bullet. Asset management is another important security practice that can help you prepare for the CMMC requirements long-term.
Do the basics right first.
You can’t secure what you don’t know you have, and your security measures should directly impact your most valuable assets (as well as the risk associated with them). Asset management is one of the most basic things you can do to improve your security program. It sets the stage for everything moving forward—including your risk assessment.
Start by tracking and categorizing resources within your organization. A good asset management practice gives businesses an understanding of the existence, access, location, and function of its important assets.
There are three types of assets that organizations need to keep tabs on.
Hardware
Think of the things you’d put a label on. This may include computers, printers, tablets, hard drives, servers, and more.
Software
Software is an asset, and it’s important to manage the purchase, licensing, implementation, maintenance, and disposal of software applications.
Data
A lot of organizations fail to realize that data is an important asset that needs the same (if not more) management as the more tangible ones. Imagine if all of the data in your organization were to suddenly disappear. Would it put you out of business? Data is an incredibly powerful asset that should be managed accordingly.
Start with a Risk Assessment
After you understand what your most important assets are, measuring the risk of compromise to those assets is the next step. The most efficient way to be proactive about your organization’s security is to perform a risk assessment. Risk assessments give you a baseline of your security program—a snapshot of your current state. Understanding this baseline is important because it tells you what gaps you have and how you can mend them, particularly as you look to enter into RFPs with the DOD that might require you to level up.
Risk assessments are meant to be barometers of change. Implementing new practices and procedures into your security program helps improve your ability to avoid and mitigate risk. And, ultimately, that’s what the DOD is trying to do with the CMMC, too.
So, get out in front of these new requirements by getting a risk assessment (especially one mapped to similar or the same controls that the CMMC assessment contains). You may not know what level you will need to be for the kinds of contracts you’ll apply for with the DOD yet. However, the more you understand the strengths and weaknesses of your own organization’s security and where the most room for improvement is, the more likely it’ll be that you’ll be prepared when the C3PAO assessment comes. Plus, it’ll help you build stronger security practices and policies in the meantime, which is never a bad thing.
Conclusion
By 2026, every request for proposal the DOD puts out will have some kind of CMMC requirement.
So, yes, you likely have quite a bit of time before the CMMC requirements are implemented into the contracts you’ll submit a bid for. But, if you can get an early understanding of what assets your organization has, and how well (or not-so-well) you secure them, it should give you time to make the adjustments that’ll get you on the right track to the CMMC level you need to achieve. A good asset management practice and a comprehensive, regulation-mapped risk assessment are the best ways to get that jump-start.
The easiest way to prepare for these new requirements is to be proactive about your security. Start with understanding what your most critical hardware, software, and data assets are. Then, conduct a risk assessment so you know what the likelihood of something bad happening to those assets are, and work to change and implement practices that can help minimize that likelihood.
By doing those things, you’ll be able to consistently work towards making noticeable improvements to your organization’s overall security practice and put yourself in a good position to level up in the CMMC framework for when the time it becomes required rolls around.
If you’d like to learn more about building a strong security program, asset management practices, risk assessments, or just improving your overall security posture in advance of CMMC requirements, reach out to us by visiting frsecure.com.