Welcome to the third post in our series with CCI where we break down the five common causes of breaches in the healthcare industry.
In this post, we’ll be discussing the second most common threat—publicly accessible login systems with single factor authentication.
With advances in development and cloud infrastructures, web applications have grown tremendously in recent years. While these platforms are sleek, user-friendly, and extremely convenient, they do pose certain security challenges.
Primarily, they are public and not all offer multifactor authentication—at least not by default.
Here is what a logon system is, the difference between single-factor authentication and multifactor authentication, and the challenge to healthcare companies posed by publicly accessible login systems with single-factor authentication.
Logon Systems
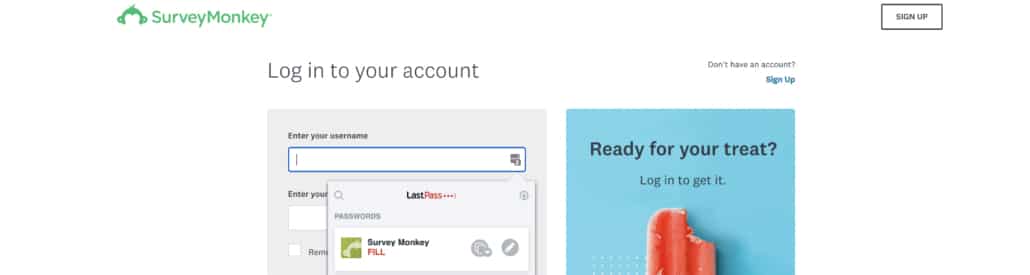
At risk of sounding too obvious, a logon system is anything you use credentials to sign into. There are endless platforms connected to the internet in today’s working world that rely on a login.
From password managers, CRMs, file-sharing services, payroll and timesheets, and things like patient portals at healthcare organizations, you log in to more platforms than you’d probably even guess on any given day.
With online systems like these, your controllables for defenses within them are often limited. To an extent, you’re at the whim of how secure the platform is or is not.
But, there are some ways that can decrease the likelihood of a mishap occurring while using these platforms. Most of the time it can be boiled down to 1) good password hygiene (which we discussed in our last post) and 2) the use of multifactor authentication.
To learn more about these methods for risk mitigation, check out CCI’s companion post.
Single-Factor Authentication vs. Multifactor Authentication
Authentication is the process of proving you are who you are trying to tell a machine, program, or software that you are who you say you are.
Single-Factor Authentication
Single-factor authentication means that you only need one method to prove you are who you say you are. As with almost all of these logon systems we’re discussing, that means a username and password.

The problem?
If an attacker can guess your password, they have access to that platform. It’s that simple.
Now, you can always beef up your password hygiene as much as possible. You can make your password 16 characters long, make it a passphrase, and mix in characters and capitalization, but that’s not foolproof.
The alternative will always be a better solution.
Multifactor Authentication
Multi-factor authentication (MFA) adds a second layer to your login.
With multifactor authentication, you not only have to log in with your username and password, but you also have to provide a secondary method proving it’s actually you. Without both, the attempted login would fail.
There are a few kinds of multifactor authentication that exist.
Something You Are
This is the most effective type of MFA because it’s nearly impossible to replicate as an attacker. However, the technology required is expensive and hard to obtain. Therefore, it’s not likely that this will exist in the platforms you’re logging into.
This includes things like iris and fingerprint scanners.
Something You Have
In terms of “bang for your buck,” there isn’t a much better option.
This type of MFA relies on something that’s in your possession—an app on your phone, a text message to your phone, an email, etc.
With this option, attackers would not only be forced to get your credentials right, but they’d also have to have access to your mobile device or email. It’s likely this will be a barricade for them.

Something You Know
This seems to be going away with the onslaught of the other two, but it’s worth mentioning.
This is a piece of knowledge that only you would know—a password, a PIN number, or a security question.
How This is Causing Breaches
There are a few ways we’re seeing single-factor authentication or mishandled multifactor on these systems leading to breaches.
The System Itself Doesn’t Have MFA
We’re at the point where this needs to be considered in your vendor search when pursuing systems.
Now, admittedly, not every platform or web app is going to have MFA available. We strongly recommend that you consider multifactor authentication a requirement when you go through the process of selecting your vendors and platforms, however.
If nothing else, at least ensure any programs you do use have MFA enabled when possible.
MFA is Not Enabled Properly or Entirely
MFA is not the default in a lot of systems. If the system you’re using is offering it, it needs to be properly enforced.
Whenever you onboard a new system or platform, go through the MFA settings and configure them so that it’s turned on for all users and required where possible.
Shared Logins or Bypassing MFA
MFA only works if it’s being followed properly.
It’s not uncommon, especially for smaller organizations, to share logins to systems and platforms.
How does that impact MFA?
If you know that you and a coworker share a login to a system, and you see a random prompt for authentication on your phone, are you going to assume that it’s your coworker and hit accept?
Blindly accepting an authentication prompt defeats the entire purpose of requiring a verification step. Be mindful of this as you decide to share access to systems.
Phishing
If you read our recent post about phishing, you remember that this is the biggest cause of breaches among healthcare organizations—and it has been for a number of years.
Multi-factor authentication can actually help you detect phishing and begin to correct for a phish much earlier. But how?
Phishing often relies on taking you to a spoofed login site where you’re expected to plug in your credentials. Say you plug your credentials into that spoofed site—it happens. If MFA is enabled, it won’t change the fact that you gave up your credentials, but it would allow you to recognize nearly instantaneously that something is amiss.
Not pushing a verification prompt should act as a giveaway that the login was incorrect, or that the site was illegitimate.
A quick side note: if your MFA platform doubles as a password manager with autofill capabilities, the system wouldn’t even recognize the site as your normal login source. That would also be a giveaway that something is off about the site.
With single factor authentication enabled, if an attacker gets credentials, it’ll be easy for them to gain access and challenging for you to notice.
Plus, then they can credential stuff your other systems with SFA and try to get access to even more platforms.
Healthcare Implications
The implications are the same as we’ve discussed before.
Reputation, business uptime, financials, and patient safety (human lives) will always be concerns when it comes to healthcare incidents.
Without MFA enabled (or even an option), you’re risking losing those critical business functions—and hurting those lives.
Wrapping Up
Multi-factor authentication is not foolproof—nothing in security is. But it is one of the simplest ways to make a drastic improvement to your overall security.
Some systems (like Microsoft) go as far as to say that their multifactor authentication blocks 99.9 percent of automated cyberattacks on platforms, websites, and other online services. Even taking that number with a grain of salt, it’s clear that MFA truly does limit the chances of a potential breach.
If you’re not employing MFA on all publicly accessible login systems, you’re begging an attacker to hop on that site, gather your credentials, and wreak havoc on your environment.
For more information about multifactor authentication, healthcare security, and information security services, visit frsecure.com.







