As I sit by the stream, I’m enamored by the fluid dynamics of the water. It trickles gracefully and effortlessly over and around the rocks, falling into and out of the deep plunge pools, circles in eddies; sometimes traveling upstream for a brief moment before returning to its original route and it ultimately reaches it’s next destination. As we know, the next destination is not the final destination, just another point in a timeless journey.
As I sit in awe, I think about my plan of attack.
The first things I always focus on are the visuals. What is the creek telling me today?
Are fish sipping bugs from the topwater? Are they laying deep, preying on nymphs following the path of the water? Do I see signs of a fly hatch or perhaps signs of fish preparing to spawn? What is the clarity level of the water? How is the cubic flow today? What are the sky conditions?
All these questions must be answered if I expect to plan a successful attack and land a trophy lunker.
This survey-focused approach I take to fishing is not dissimilar to how cyber attackers landscape their targets.

How Does This Relate to Cyber Attacks?
When attackers target humans for cyber attacks, the science is remarkably comparable.
You have to recon your target, understand their habits, know what they are interested in today, and develop a successful plan of attack accordingly.
That plan of attack is synonymous with fishing a realistically tied fly and perfect presentation. You have to know what your target wants to take and develop a presentation that mimics reality. And let me to you from experience— in both worlds, presentation is key.
A fish doesn’t become a lunker by being dumb. Catching a real trophy is challenging because they are smart. That’s how they’ve made it so long in the water without being harvested by a fisher—human or wildlife included. A real trophy knows how to identify predators and avoid them. They also know how to carefully select their food with the lowest amount of risk possible. This is why they’re called a trophy in the first place—you have to be a master of your skill to catch one.
We, humans, are just the same in the eyes of an attacker. We may think we are on top of our game and aren’t going to be tricked into another scam, but it happens every day. Attackers are smart. They know our habits and interests. They are very good at understanding human psychology and use this to execute a brilliant presentation in a well-built attack.
Comparing This to a Recent APT Attack
This leads me to the topic of the day. Let’s talk about how a recent APT attack targeted and landed some real trophies. You may recall in a recent Hackle Box episode we briefly reviewed a recently discovered campaign believed to be executed by North Korean threat actors that is specifically targeting security researchers.
This APT attack campaign is a little bit different than your typical targeting through email, SMS, or phone call as they are preying on folks scouring the web for research and information regarding new vulnerabilities and exploits.
The threat actors started by building some Twitter profiles and working to build credibility in the community. Alongside this, they created some research websites and began populating a YouTube channel with “apparent” proof-of-concept videos outlining their so-called exploits. The Twitter accounts were then utilized to retweet posts from other accounts they controlled to share links to their research blog and exploit videos.
They put a lot of work into all these things to make them look legit and build credibility. There were farms of users to follow their research Twitter accounts and to interact with themselves and unsuspecting researchers.
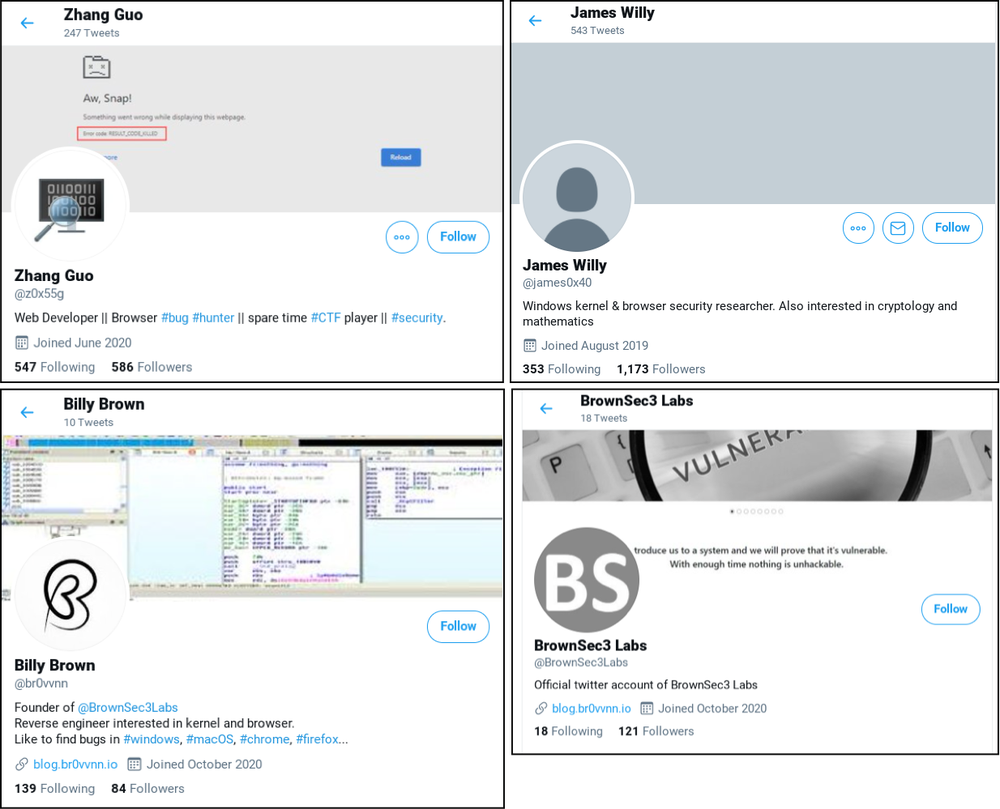
Bogus LinkedIn, Discord, and other profiles were built and used as well.
They also populated their blog articles with feedback and had constant interaction with other researchers—some bogus and some valid. The content posted on the blog looked genuine and well-developed. And, from what we know, they were posting some legitimate and useful content there.
However, they were also faking some of the information.
Specifically, they claimed to have an exploit for a Windows Defender vulnerability (CVE-2021-1647) that would permit the attacker to bypass the program and launch a command shell. This exploit did not exist, and their video showing the PoC was busted as being faked.
Why do this?
We know that when this vulnerability was released researchers, pen-testers, blue teamers, and attackers wanted to know how to exploit it. By being the first to the punch and getting a Proof of Concept (PoC) of the exploit online, it’s a surefire way to drive traffic to your malicious website.
It worked—they caught more than a few. Perfect bait and perfect presentation.
The Payload
So what was the payload?
This is where things get even more interesting. There are actually two.
First, some visitors were (un)lucky enough to have their systems compromised just by visiting the malicious site. It was observed that a malicious service was installed on the system that served as a command-and-control beacon. Reports say that at the time the victims’ browsers were fully up to date—I smell a zero-day. We do know since this report a few Chrome zero-days were revealed, and we even recently worked on a case that outlined this exact scenario.
In the other mechanism of this APT attack, the attackers would engage researchers who commented or interacted with them on their blog or Twitter to see if the victim was interested in collaborating on a research project. If the victim accepted the offer, the attackers would then share a Visual Studio project with the victim that contained a malicious DLL—executed through VS Build events that were (you guessed it) a command-and-control beacon.
Takeaways
The moral of the story is that social engineering can adapt to all shapes and forms. We tend to think of social engineering as phishing emails, but it can and often is so much more than that. Our attackers understand the principles of hooking a trophy lunker very well. Bait and presentation are key.
My immediate advice: don’t trust unknown sources, vet your sources to the highest possible extent, work in a sandbox when researching, and network isolate.
The IoC’s
Courtesy of Google’s Threat Analysis Group (TAG)
https://blog.google/threat-analysis-group/new-campaign-targeting-security-researchers/
Actor Controlled Sites and Accounts
Research Blog
- https://blog.br0vvnn[.]io
Twitter Accounts
- https://twitter.com/br0vvnn
- https://twitter.com/BrownSec3Labs
- https://twitter.com/dev0exp
- https://twitter.com/djokovic808
- https://twitter.com/henya290
- https://twitter.com/james0x40
- https://twitter.com/m5t0r
- https://twitter.com/mvp4p3r
- https://twitter.com/tjrim91
- https://twitter.com/z0x55g
LinkedIn Accounts
- https://www.linkedin.com/in/billy-brown-a6678b1b8/
- https://www.linkedin.com/in/guo-zhang-b152721bb/
- https://www.linkedin.com/in/hyungwoo-lee-6985501b9/
- https://www.linkedin.com/in/linshuang-li-aa696391bb/
- https://www.linkedin.com/in/rimmer-trajan-2806b21bb/
Keybase
- https://keybase.io/zhangguo
Telegram
- https://t.me/james50d
Sample Hashes
- https://www.virustotal.com/gui/file/4c3499f3cc4a4fdc7e67417e055891c78540282dccc57e37a01167dfe351b244/detection (VS Project DLL)
- https://www.virustotal.com/gui/file/68e6b9d71c727545095ea6376940027b61734af5c710b2985a628131e47c6af7/detection (VS Project DLL)
- https://www.virustotal.com/gui/file/25d8ae4678c37251e7ffbaeddc252ae2530ef23f66e4c856d98ef60f399fa3dc/detection (VS Project Dropped DLL)
- https://www.virustotal.com/gui/file/a75886b016d84c3eaacaf01a3c61e04953a7a3adf38acf77a4a2e3a8f544f855/detection (VS Project Dropped DLL)
- https://www.virustotal.com/gui/file/a4fb20b15efd72f983f0fb3325c0352d8a266a69bb5f6ca2eba0556c3e00bd15/detection (Service DLL)
C2 Domains: Attacker-Owned
- angeldonationblog[.]com
- codevexillium[.]org
- investbooking[.]de
- krakenfolio[.]com
- opsonew3org[.]sg
- transferwiser[.]io
- transplugin[.]io
C2 Domains: Legitimate But Compromised
- trophylab[.]com
- www.colasprint[.]com
- www.dronerc[.]it
- www.edujikim[.]com
- www.fabioluciani[.]com
C2 URLs
- https[:]//angeldonationblog[.]com/image/upload/upload.php
- https[:]//codevexillium[.]org/image/download/download.asp
- https[:]//investbooking[.]de/upload/upload.asp
- https[:]//transplugin[.]io/upload/upload.asp
- https[:]//www.dronerc[.]it/forum/uploads/index.php
- https[:]//www.dronerc[.]it/shop_testbr/Core/upload.php
- https[:]//www.dronerc[.]it/shop_testbr/upload/upload.php
- https[:]//www.edujikim[.]com/intro/blue/insert.asp
- https[:]//www.fabioluciani[.]com/es/include/include.asp
- http[:]//trophylab[.]com/notice/images/renewal/upload.asp
- http[:]//www.colasprint[.]com/_vti_log/upload.asp
Host IOCs
- Registry Keys
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\KernelConfig
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\DriverConfig
- HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\SSL Update
- File Paths
- C:\Windows\System32\Nwsapagent.sys
- C:\Windows\System32\helpsvc.sys
- C:\ProgramData\USOShared\uso.bin
- C:\ProgramData\VMware\vmnat-update.bin
- C:\ProgramData\VirtualBox\update.bin
If you or your organization needs assistance in understanding this type of APT, enacting on some of the recommendations mentioned above, or with any security-related questions, please do not hesitate to reach out us at frsecure.com.







