Information security is a living, breathing process that’s ongoing, it’s a life cycle. Without a life-cycle approach to information security and its management, organizations typically treat information security as just another project. Projects have a beginning and ending date. Once completed, resources are shifted to the next hot initiative and focus shifts away from security. Information Security is a business decision after all and who makes business decisions for organizations? Hint – it’s NOT the good folks in IT. Understanding and managing risk for an organization is a critical component of information security. Once Executive Management is informed of an identified risk they can decide how they will address the risk so the information security life cycle can begin. This will eliminate the “information security is just another IT project” mentality and help give direction and support so that the focus can be on the organizational goals.
4 Basic Options to Decide How to Address an Identified Risk.
| Accept [av_font_icon icon=’ue812′ font=’entypo-fontello’ style=” caption=” link=” linktarget=” size=’40px’ position=’left’ color=” admin_preview_bg=” av_uid=’av-21gs1vd’][/av_font_icon] | The identified risk is understood and the decision is made to continue as is. |
| Reduce[av_font_icon icon=’ue887′ font=’entypo-fontello’ style=” caption=” link=” linktarget=” size=’40px’ position=’left’ color=” admin_preview_bg=” av_uid=’av-1q8n0ft’][/av_font_icon] | Measures are put in place that will reduce the chances andor the impact of the risky activity. Firewalls, training, and policies are examples of compensating controls. |
| Transfer[av_font_icon icon=’ue896′ font=’entypo-fontello’ style=” caption=” link=” linktarget=” size=’40px’ position=’left’ color=” admin_preview_bg=” av_uid=’av-1258l7d’][/av_font_icon] | Purchase insurance or offload the risky behavior to a more qualified party. |
| Avoid [av_font_icon icon=’ue814′ font=’entypo-fontello’ style=” caption=” link=” linktarget=” size=’40px’ position=’left’ color=” admin_preview_bg=” av_uid=’av-mlxzix’][/av_font_icon] | Stop doing the risky behavior all together. |
4 Steps of the Information Security Life Cycle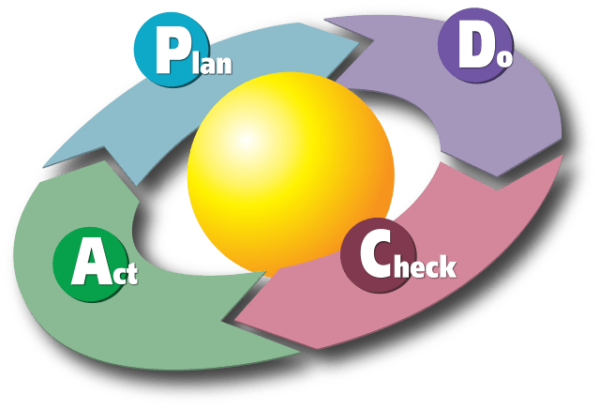
Step one – Plan
Involve senior management as well as stake holders and department managers. Information security is not just an IT issue, the whole organization needs to be on board in order to have a strong information security program. Form a committee and establish agreed on direction.
| Action | Reasoning |
| Establish management’s commitment | They are ultimately responsible for ensuring the organization is protecting its assets. |
| Establish an oversightsteering committee | Gathers consensus from stake holders. |
| Determine business needs | Information Security needs to align with organization initiatives. |
| Know your threat profile | Understand where probable threats might come from. |
| Understand the organization’s risk tolerance | Determined by executive management |
Step two – Do
Assign specific responsibility to individuals, determine timelines and desired results. Develop a “cookbook” that lays out policies, standards, procedures, and guidelines that can be followed to maintain a strong information security program. Just as parts of “recipes” may change over time, parts of your information security program may change as well.
| Action | Reasoning |
| Assign roles and responsibilities | Hold people (including management) accountable to accomplish what management has directed. |
| Develop Implement Policies, Standards, Procedures, and Guidelines | The organization’s “cookbook” for securing information assets. |
| Implement solutions (administrative, technical and physical) | Per your “cookbook” |
| Establish goals and metrics. | To measure the effectiveness of your approach, are you getting better or worse. |
Step three – Check
After solutions are implemented, review the audit findings to determine if the desired results are being achieved.
| Action | Reasoning |
| Follow procedures and standards | Ensures the organization’s recipes are followed. |
| Carry out audits | Are we meeting the agreed upon goals and metrics? |
| Manage SLAs per organization standards | Are we meeting the customer’s (internal or external) agreed service levels? |
Step four – Act
These actions should be based on your audit results, with adjustments made as needed. Circle back to the Planning step and run through the process again until the threat is reduced to an acceptable level.
| Action | Reasoning |
| Review audit results, collected metric values, and SLAs. | Used to determine effectiveness of approach |
| Carry out quarterly meetings steering committee | Report audit findings, update executive management on the effectiveness of implemented risk reducing solutions. |
| Develop improvement steps and integrate back into Step One – Plan phase. | Follow the process for these new steps back thru the 4 phase. Continue to do this for each risk identified until the risk is at a management approved acceptable level. |
Performing a comprehensive risk assessment will allow executive management to make a sound, risk based decisions. The findings from the assessment will help give direction and a roadmap to follow to ensure identified risks are addressed. A risk assessment and roadmap will also help to eliminate starts and stops on initiatives that can cause repetitive work and cost more than it should, with diminishing results. In the end, information security is a constant cycle of planning, doing, evaluating, and acting. And once you’ve completed that cycle once, you get to start over and complete it again, and again, and again. Just as security threats are constantly evolving and changing shape, so must your information security program. We here at FRSecure want to help simplify this process and help fix this broken industry, so feel free to contact us. We would love to help solve your information security needs.






