The focus of my role here at FRSecure is network architecture reviews and vulnerability scanning. I have noticed a surprising trend over the course of the last year; very few businesses are effectively using subnetting as a security mechanism! I often probe deeper on this subject to hear the rationalization, simply because it intrigues me. This is what I found.
Why Don’t Businesses Use Subnets?
Some businesses point to segmentation in Active Directory as the reason for the file server not being segmented from other network traffic, others segment voice and data for Quality of Service. I would say the most common answer is that the company’s network was inherited from the previous administrator. When the incoming administrator took over they did not make any adjustments or advances to the network, they just kept rolling with what had been working thus far. The issue here isn’t the understanding of how segmentation provides benefits to aspects of the network; but, either a lack of knowledge of the full benefits of segmentation, or how to properly segment their network.
Why Should Your Business be Subnetting?
Why should a receptionist workstation be able to communicate with a workstation in HR? What if that same user can access a SQL server, or network equipment? These are common occurrences in small to large enterprise networks, and pose a significant risk to information security. Typically, significant risks are equated with large dollar figures to implement some shiny new box that fixes the issue…and saddles your company with an expensive maintenance contract, warranty, and support. Great news! Subnetting is neither shiny or new, it is a cost-effective way to isolate network communication, and the technology is already built into managed network equipment. There is some labor involved, mostly research and designing time, but this results in a great deal of control to the network.
How Should You Set Up Your Subnet?
Not having subnets would be similar to renting a warehouse and filling it with desks that are randomly assigned each morning. Imagine the chaos that would follow? Nobody would be able to hear themselves think! Everyone would be able to hear everything that everyone else is saying, but they would only be able to hear parts of relevant information. Your organization probably provides separate work-spaces based on the level of information that is accessible. There is a natural order to how business units interact with each-other, what information they can discuss, and segment office space. This reduces the chance of someone overhearing a sensitive discussion between HR and an employee, or someone in sales having access to file-cabinets in the finance department. Subnets allow you to take your network “warehouse” and turn it into well organized “office space.”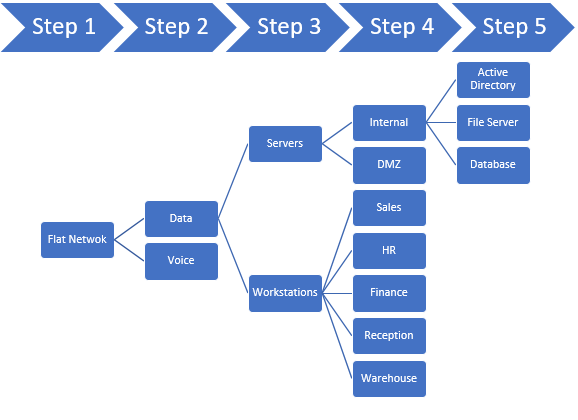
I recommend implementing subnets to any client I feel has insufficient segmentation in their network. It is a cost-effective measure that provides value to other technical controls, vulnerability scanning, logging, alerting, and can even limit exposure to malware. Throughout this Network Security series I will be providing more high level overviews of network controls to help beef up your network with basic controls such as subnets. I will also be providing technical examples for your IT staff that will have specific implementation suggestions that can be used to help secure your company’s network. If you have any questions about how to properly implement subnetting into your company’s network or want to know more about subnetting, contact us or leave a comment in the comments section!







Great information Matt. Thank you for sharing your subnetting experience. ;<)